NOKIA - Insecure Direct Object Reference
Hi all,
Recently i have found Insecure Direct Object Issue on Nokia. I have already reported this issue and also got fixed.
Thanks to Nokia developer Team. They have listed my name on Nokia Hall Of Fame List on below mentioned URL:
http://www.nokia.com/global/security/acknowledgements/
Before we start discussing the issue we will first look into what Insecure Direct Object Reference is?
What is Insecure Direct Object Reference?
The Insecure Direct Object References represent the flaws in system design where access to sensitive data/assets is not fully protected and data objects are exposed by application with assumption that user will always follow the application rules.
Insecure Direct Object Reference is an attack where attacker who is an authenticated system user, simply changes a parameter value that directly refers to a system object or another object the user isn’t authorized for.
(Note:
***Authentication:***Authentication verifies who you are.
Authorization: Authorization verifies what you are authorized to do. )
OWASP Definition For Insecure Direct Object Reference
A direct object reference occurs when a developer exposes a reference to an internal implementation object, such as a file, directory, database record, or key, as a URL or form parameter. An attacker can manipulate direct object references to access other objects without authorization, unless an access control check is in place.
How to identify Insecure Direct Object Reference ?
Identifying this vulnerability is slightly more difficult using Automation tools than other vulnerabilities because to exploit this vulnerability you not only need to identify the flawed interface but also need to predict the pattern to identify an secure object like File name, User Id or Customer Id etc.
So lets Begin with how i have found Insecure Direct Object Reference on Nokia:
Nokia has a functionality called “Request Details” where user Request Invoice detail and this details has been saved in “Requests waiting for response” Section of his profile.
This request can be viewed by an User. Below is the URL for the same:
https://ap.nokia.com/APPortalExt/mycompany/requests.aspx?id=28176
Below is the Screenshot For the Same:
[caption id=“attachment_116” align=“aligncenter” width=“458”]
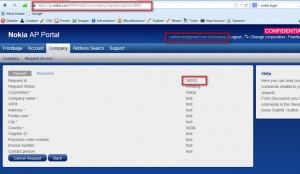
After analyzing above mentioned URL i have noticed that the parameter id is number.
I have easily change this to valid request number and i was able to see other Invoice details which was requested by another User.
Below is the Screenshot For the Same:
[caption id=“attachment_118” align=“aligncenter” width=“373”]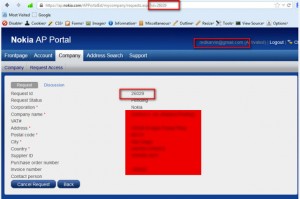
Nokia Mail

Nokia Hall Of Fame List

Prevent Insecure Direct Object References :
In simple terms the protection we need is to
- Minimize user ability to predict object IDs/Names
- Don’t expose the actual ID/name of objects
- Verify user authorization each time sensitive objects/files/contents are accessed
Recent Reply From Nokia (4 Sept 2013)
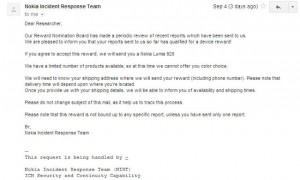
Generous Reward Lumia 920 from Nokia (Fastest Delivery from Nokia Received Within 3day :) )

